What do I need to do about the Meltdown and Spectre vulnerabilities?
Meltdown and Spectre refer to a couple of classes of possible weaknesses, or "vulnerabilities," in the server chip design used by processor makers Intel, AMD, and ARM. So far, there's no evidence that an attacker has taken advantage of these vulnerabilities, but research has shown that it's possible. See this Microsoft support article for details of how this might happen.
If your VPS or Dedicated Server is affected by these vulnerability issues, you'll need to install a Windows patch. For more information, read below.
Am I Affected?
Self-Managed Servers
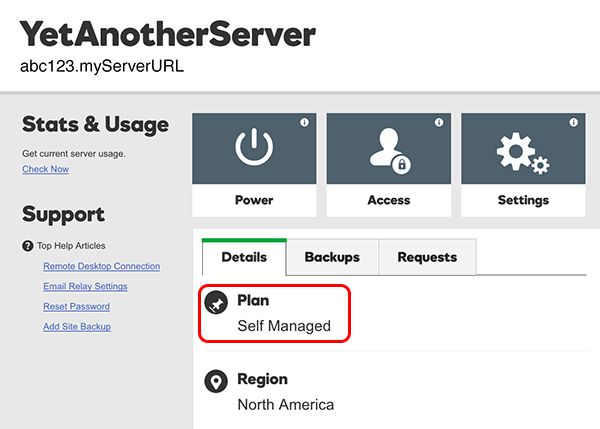
If you have a self-managed VPS, or a self-managed Dedicated Server, you are affected and need to install a Windows OS patch. To check if you have a self-managed server, on your My Products page, click Servers, and next to your server click Manage. If your Plan type is Self Managed, you need to install the patch.
Managed or Fully-Managed Servers
If your plan type is "Managed" or "Fully Managed," and you have turned off Windows Updates, you are affected. You need to turn Windows Updates on and initiate the updates to complete the patch. If you're not sure and want to check, see this Windows Update FAQ.
For "Managed" and "Fully Managed" plans, Windows Update is turned on by default - so if you haven't changed this for your plan, we've already taken care of this for you and you are not affected.
Other Windows Hosting Products
For all other GoDaddy Windows hosting products and plans, such as Windows Shared Hosting, we've already patched the servers and you are not affected.
Install the Windows Patch
In this Microsoft support article, follow Steps 1 and 2 under What steps should I take to protect my devices?. We'll take care of hardware (firmware) updates as mentioned in Step 3. You'll need to connect using the remote desktop.
Effect on Server Performance
Based on published data and our preliminary testing, we expect 10% (or less) impact to server performance. For more, see this article at intel.com.
More info
You can learn more at the National Vulnerability Database (NVD) website:
- For information on Spectre, see CVE-2017-5753 and CVE-2017-5715
- For information on Meltdown, see CVE-2017-5754